Disclaimer: not paid, not sponsored, etc etc. Just a fan 🙂
Hey everybody, HuskyHacks the hacker/hiker here! And maybe a little huskier than usual now that I think about it. Post AT hiker hunger + quarantine life is not a good combination. Time to lace up the running shoes again.
The Intro
After getting back from the AT and taking a few days to decompress, it was clear pretty quickly that I needed something to do. A few days of couch-potato YouTube video sessions may have been the immediate antidote for my post-trail feeling of restlessness, but it was not the long term solution. After reclaiming my desktop workstation and setting everything back up, I turned my sights towards eLearnSecurity Penetration Testing Professional (PTP) and its corresponding certification, eLearnSecurity Certified Professional Penetration Tester (eCPPT).
Before I go any further, it might help for me to cover why exactly I wanted to go after this cert. I passed OSCP in February of this year to bookend about 9 months of red-side cybersecurity study. With plans to leave for the AT in March of this year and an estimated completion time in September, passing OSCP meant that I would have a door-busting certification in my pocket for when I got home. The problem with this plan, however, was that I’d be spending a long time away from hands-on-keyboard currency in the field: a serious consideration for anyone who wants to be the strongest practitioner that they can be.
My proposed solution for this would be to take PTP after completing the trail, get my head back in the game and hands back on the keyboard, and then proceed to look for jobs. That way, I could set off on my great adventure unconcerned about returning to the field without any currency.
Well, we all know how that turned out.

So my plan was to take this course anyway when I got back from the Trail. I just, ya know, didn’t think it would be in April…
In any case, this course gave me something to focus my energy on and, judged solely on that criterion, it knocked it out of the park. I registered for the course and received access to the materials on March 26th, began the exam on April 10th, completed the exam and submitted my report on April 14th, and received my passing notification on April 22nd. My thoughts about the experience are what follows in this post.
One final note: the comparison between PTP and OSCP in the above paragraph was needed for context as to why I was going to take PTP in the first place, but that is where my comparison of the two will end. PTP is a stand-alone certification and deserves to be judged on its own merits, not necessarily against another cert in the field. They both have pros and cons, they both do things very well and could use improvement in other areas. And additionally, I took the previous version of OSCP before its big update (in fact, the course update dropped three days after I had submitted my report for grading). I will simply say that I’m fortunate enough to have taken both and, if you are in a position to do the same, I think there’s tons of value to be found if you do so.
And for my military/veteran readers, I’ll leave the comparison alone with a final analogy: to me, OSCP was boot camp, and PTP was A-School.
The Course
I have nothing but glowing remarks about the course setup itself.
Right from the get go, you have immediate access to the materials in a gorgeous student learning portal. Whenever you want to take the exam, you click a link and you’re in. Every learning module has an expansive slide deck that does every topic justice. If you have the Elite version of the course, you can download these slide decks to store offline, although I didn’t find it necessary as you’ll have lifetime access to the training after purchase.
I couldn’t help but think that this is the way all online learning should be: quick response time, immediate feedback, no hassle of scheduling exams or waiting to receive materials. eLS absolutely nailed the execution here.
The user experience does its job in that it does not detract from learning the material at all, which is important because…
The Material (My God, the Material)
The content of this course is expansive! There are 5 core modules and 2 bonus ones in the Elite version, with the meat of the course residing in the Network Security module.
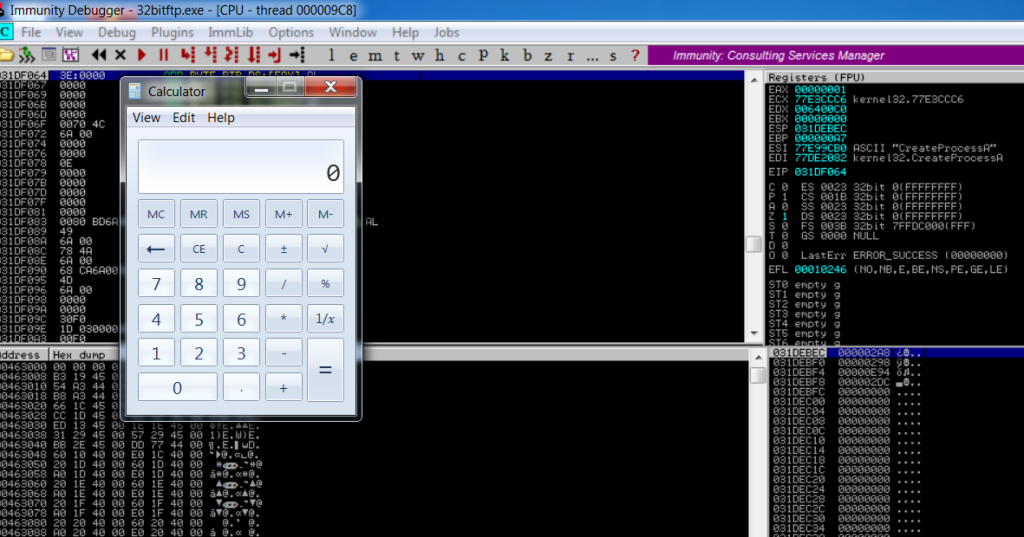
First up is the System Security module, which covers debugging, reverse engineering, and the dreaded buffer overflow. This module is one of the most technically comprehensive and might be overwhelming at first if you have no experience with this topic, but the explanation of system architecture and how computers use memory is worthy of merit. I entered this module with the knowledge of how to perform a 32-bit buffer overflow in very lenient circumstances, but with little understanding of how exactly that attack can trick a computer into executing something you want it to execute. Not only does this module cover the basics of the stack and memory address allocation, but breaks down what actually happens down at the OS level when memory is PUSHed to the stack or POPped off the stack. You even write shellcode from scratch (yes, from scratch, not by telling MSFVenom to spit out something to add into your script), which pretty much blew my mind.
The ‘lab’ for this module is really just a Windows 7 x86 VM that you can fire up to play around with different debuggers, do object dumps and build your custom shellcode. You’ll follow along with the lessons and perform the actions, but there are no dedicated lab scenarios like there are later in the course for the Network Security module, for example. This isn’t a huge deal, but you do still burn hours in the lab while using this VM; my tip to all of you that maybe want to save a few hours of lab time in this module is to go find a dusty old Windows 7 x86 ISO and stand up your own Dev machine. You’ll be able to find all of the tools used in the lessons online and open-source, and it’s also good practice to build a Dev machine to tailor exploits to the target environment.
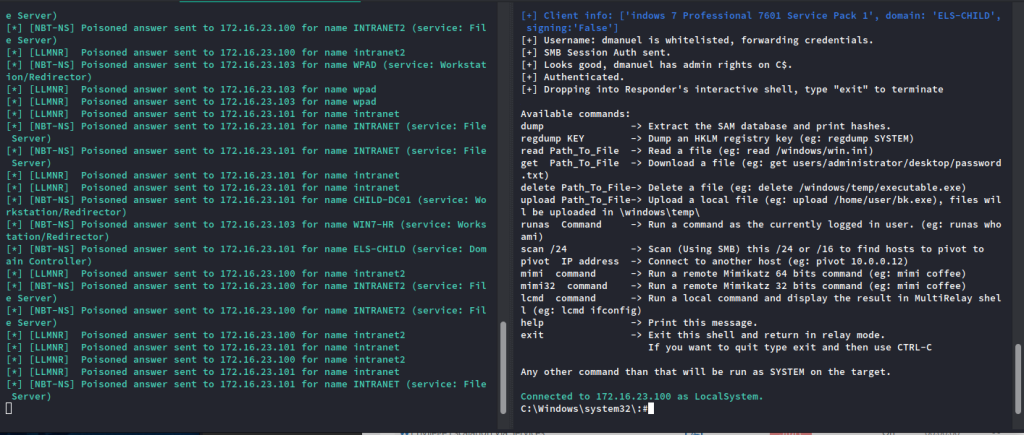
The meat and potatoes of this course is next up: the Network Security module. This is everything you dreamed you’d be doing as a pentester, like enumerating systems, researching exploits, launching attacks, post compromise info gathering, and privilege escalation. This module is not as technically deep as System Security, but make no mistake- it’s the reason you’re here. This is the ‘tools of the trade’ module; it has the best labs in the course, is overall the most fun, and definitely where you’ll learn the most. I’m glad that I have lab time left over, because there’s a good chance that I’ll go back and do these labs again someday. This module will bring you from initial recon all the way through foothold exploitation, then covers AD attacks, which is where the money is made in internal pentesting. It is absolutely thrilling to do some of the tasks that the labs outline, like ICMP redirect with Scapy and LLMNR poisoning. My tips here are simply to take great notes, copy the syntax that works into a cheat sheet to perform later, and enjoy the ride.
Up next, we have Powershell for Pentesters. And, well…
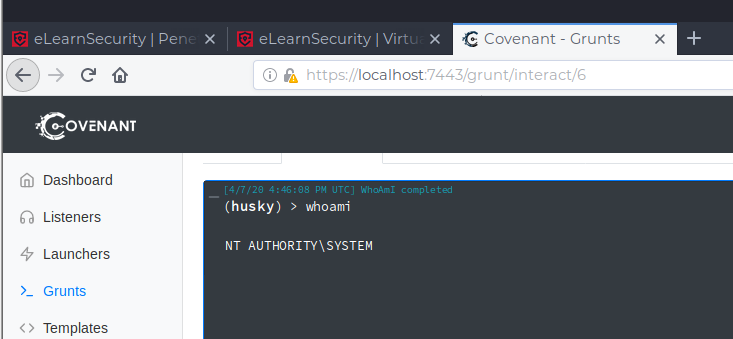
This module, while crucial in terms of real world application, left me a little unsatisfied. The content is great, and the labs are great in theory, but the execution of the labs got a little wonky for me. I’m running the latest build of Kali 2020.1, which meant that a) they done killed Python2 and b) all legacy tool sets from earlier Kali builds are going to be unstable at best. In these labs, the intended method of attack is to use Powershell Empire, Impacket, and Metasploit to gain a C2 foothold. But I struggled to get a version of Empire to work on my new Kali build. Many hours later of troubleshooting later, I was able to get an instance of Empire running, but then found that it wouldn’t work with Impacket. I ditched Empire completely and learned how to install a newer C2 suite, Covenant, from scratch. And this worked! …until I couldn’t transfer the C2 foothold to Metasploit because there was no cross compatibility with Covenant. Arg!
I got the lab to work and completed it, but it cost a lot of time and frustration and I had to circumvent some of the true objectives. But I learned how to build a newer C2 suite on the fly and got to use it to do some really cool stuff, so it wasn’t all bad. And most importantly, troubleshooting and fixing on the fly is kinda the name of the game in pentesting. Nothing is going to work right out the box every time.
After Powershell, we have Linux Exploitation. I felt very comfortable in this module after completing lots of Hack the Box machines and the OSCP labs, but there’s still stuff to be learned here. To round out the core modules, Web App Security covers the very beginning of Web Application exploitation. A tip for success on the exam: do not skimp on Web Application testing. I’ll cover more on this later, but for now, just make sure that you have a good understanding of all web based vulnerabilities, not necessarily the ones that will land you a shell on the server.
(Edit: the next section was actually incorrect initially; Powershell for Pentesters and Ruby & Metasploit are the extra modules in the Elite version, and Wi-Fi Security is available in all versions. Updated with the correction.)
The two final modules are Wi-Fi Security and Ruby & Metasploit. And, to be honest, I’ve yet to actually complete either of these. I knew that the extra modules would not be on the exam and I considered it bonus points to learn how to write Metasploit modules on the fly in Ruby and perform WPA2 cracking attacks. I’m treating these sections as an epilogue to the exam and plan on completing both of them next week for added learning. Completing the exam was my number one priority; I should have no problem completing these two modules on my own time now.
My final tips for the course itself: just because the modules are set up in a specific order does not mean you have to complete them in that order. I got the most out of the course by doing the modules in this order, which I am deeming the HuskyHacks Supreme PTP Learning Module Sequence (patent pending):
- Network Security
- Linux Exploitation
- Web App Security
- Powershell for Pentesters (if you have the Elite version; complete the labs to the best of your ability)
- System Security (pay attention to the Buffer Overflow)
- (Take the exam?)
- Wi-Fi and Ruby (if you have the Elite version)
Whew! I wasn’t joking when I said the content is expansive. But once you’ve made it through the modules, it’s time for…
The Exam (dun dun DUUUNN)
Psst. Hey kid! Want PTP exam spoilers?
Well, go somewhere else! I worked hard for this cert and you will, too.
I started my exam at 8am on Friday, April 10th. Right from the outset, the exam treats the scenario like a real penetration test. Do not take this setup lightly; this is not a game of capture the flag or a race-to-root smash and grab. You’re expected to perform a thorough penetration test and document all of the results. Remember when I said to pay attention to all of the methods of web application exploitation, not just the ones that could get you a foothold? On the exam, leave no stone unturned. If you found it in real life, even if it’s something small, you would report it to the client, right? Treat the exam the same way and you’ll smash it.
In very general terms, this is how the exam went:
Day 1
I sat down, bright eyed and ready to crush the exam, cranked up the Lofi beats, and went to work!
With 7 days ahead of me, I felt very little stress related to the time hack for completion. I metered out my days to work something similar to normal working hours, with a few breaks to stretch and eat, and found this to be beneficial to my productivity. I performed all initial recon and found some quick wins, documented my results, and called it a day.
Day 2
The second day of the exam revealed one of the principle challenges; pivoting. If you have never needed to pivot through networks, there are a few ‘gotcha’ moments that will make you think laterally. For reference, check out this blog post for a fantastic overview of how to pivot practically. In short, a lot of your tool functionality is going to change as soon as you pivot, but there are still tons of ways to get the info that you need. Day 2 also reacquainted me with my tendency to overthink things, and reminded me that post compromise enumeration is critical if you are not just attacking a single, static target.
Day 3
At the end of day 2, I had identified the host that is vulnerable to a buffer overflow. I was so excited to crush this host that I even stayed up a little later prepping the tools to launch the exploit in the morning. My POC worked flawlessly the night before, so it was very shocking when I launched my exploit the next morning and received crickets in return.
I ran through each step of the process and had nailed all of the inputs/outputs. What was I doing wrong?
I burnt a whole day trying to troubleshoot the buffer overflow, but finally got it in the evening of day 3. And though I can’t say how I managed to pull it off, I can say that it involved a lot of fervent Googling and maybe a sacrificial clump of hair or two. The solution here was an exercise in thinking laterally, and I’m actually grateful that I had to think on the fly here because it taught me some critical lessons. At the close of day 3, I had a lot of results to report but was missing the actual win condition that the exam details in the engagement letter. The siege continues!
Day 4
Day 4 was a scouring of each host to find the missing pieces. After tearing apart hosts that I had already rooted, chasing rabbit holes that I had no business chasing, wondering if the boxes I hadn’t rooted yet held the keys, and drawing my own Charlie Day cork board graph of madness, a moment of clarity led to the final piece of the puzzle falling into place.
And after some final privilege escalation, I had achieved the win condition for the exam. I reviewed all of my proof of concept steps, made sure that I had the screenshots for the report, and killed the exam VPN. The next morning, I wrote and submitted the report.
The ‘So What?’
A week and a day after submitting the report, I got the email that I passed. And, much to my delight, I received the gorgeous new version of the eLS certifications in PDF format.

So for a rollup: do I think this cert is worth it? Absolutely. It would be worth it if it was priced even higher than it is currently. I know that the cert’s price point may be steep, but the hands-on practical knowledge you will come out of this course with will more than pay for itself in the long run. Imagine landing a pentesting interview as a new practitioner; imagine the look on your interviewer’s face when they realize that you know both external AND internal methodology. Imagine their surprise when you don’t flounder on how to perform an LLMNR poisoning attack. This course will teach you that, and I stand by it as a fantastic, well-rounded array of practical exercises and theoretical knowledge.
So, final tips for the course and the exam:
- Build a Dev machine to perform the System Security exercises on- it’s good practice and saves you precious lab hours!
- The Web App section is not too bad, but don’t ignore what it has to teach.
- On the exam, if you find it, report it. It doesn’t matter if it gets you closer to root or not.
- Network Security is the meat and potatoes of the course; dig in!
- Practice pivoting!
- Above all else, have fun and enjoy this course! We should all be so lucky if we get more intro/intermediate level courses that are this solid.
If you have any questions, feel free to light up my inbox!


5 replies on “Back in the Saddle: eLearnSecurity PTP Review”
[…] a couple of whirlwind months, I was forced to return home from the Appalachian Trail, took some great certification courses, moved to the city that will be my home for the next five years, landed an amazing gig at an […]
LikeLike
[…] plus one for including Covenant, because I was about done with Empire. If you recall, my PTP review included a section about how difficult the Powershell module was due to its reliance on Empire, […]
LikeLike
[…] after returning from the AT, so I ended up knocking it out a lot sooner than I had anticipated. Check out the review for more information; in short, it was a great course that built a lot on the skill base from […]
LikeLike
[…] I want to say I’m only familiar with Matt Kiely aka HuskyHacks due to his blog for the eCPPT. https://huskyhacks.dev/2020/04/24/elsptp/. I enjoyed his other blog posts and ended up following him on twitter […]
LikeLike
[…] https://huskyhacks.dev/2020/04/24/elsptp/ (eCPPT Review) […]
LikeLike